Two things happened today that inspired me to write this post tonight.
- A brief back-and-forth on Twitter with @kaigani where I outlandishly claimed that Facebook Connect is a phishing scam waiting to happen
- The warning of another Twitter scam that typically exploits the layman‘s inability to spot a fake URL.
Facebook and Twitter both offer authentication services arguably known as “single sign-on”. Facebook Connect is a proprietary system, and Twitter offers a system based on the OAuth standard. These services do something quite marvellous – They allow you to authenticate with a another website without the third party ever seeing your password. What’s makes it even more handy is that you’re probably already signed in to these popular services, so you may not need to enter your password at all. The problem is when you do.
If the mother service decides you aren’t logged in, it will have to present you with a username/password prompt just as if you were entering the main site. Here’s an example Facebook Connect popup:
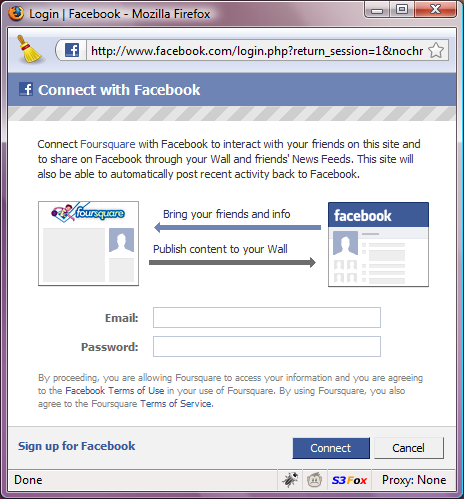
A complacent user is likely to fill in these credentials without checking whether this page belongs to Facebook. This is the classic Phishing model, and I would argue that it is made worse by the additional trust the user may place in this familiar system. Furthermore, some implementations present this dialogue in a overlay form where no address bar appears at all.
There are various lines of defence available to the user at this point, and they are all in the browser.
1. The URL
Most phishing scams use cleverly manipulated URLs that can easily trick an untrained eye. The fact is that the address bar and the URL are (from an end-user perspective) quite technical aspects of using the Internet. These “connect” dialogues are prone to this problem, and to make it easier for the phishing gangs they don’t have to recreate the whole home page, just one small window. Even for Internet professionals, an accurately copied design may provide little reason to glance at the address bar.
2. The SSL Certificate
In the unlikely event that hackers have infiltrated your ISP, you still have the server certificate to ensure the site is legit. Observant readers will notice that the above image does not show a secure page. This is a failing of the vendor and of Facebook. A secure page does exist for Facebook Connect [see below] but Facebook should not offer standard HTTP at all and in this example the vendor should have used the SSL version.

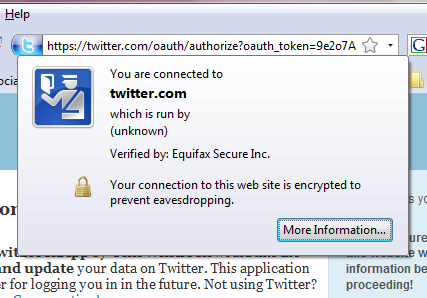
Twitter also fails to restrict their authentication screen exclusively to SSL. To make matters worse their SSL screen does not contain full identity information (see below). Many Twitter apps don’t use the SSL page, and in fact the application settings page for developers lists the OAuth service URLs as HTTP variants only.
Is this a technology problem, or a human problem?
These scams exploit ignorance and complacency – Two things that user-friendly web services like these can only perpetuate. All the cryptography magic and clever security models behind these services can’t actually prevent phishing scams, and as they become more common and more trusted, perhaps they just make phishing scams easier to pull off.
I’m not convinced these problems can be solved by technology; at least not by technology in the websites themselves. I think this can only be solved by something that sits between the user and the trap – For example: the web browser, your ISP, or the HTTP protocol itself.
- Chrome and IE8 both offer a neat address bar feature where the host name is bolder than the rest of the URL making fake URLs much easier to spot;
- Firefox has more obvious server certificate and identity information, makes more of song and dance about invalid certificates and shows the host name in the status bar;
- Various browsers offer warnings of known scam URLs and no doubt many ISPs aid this effort
However, these features still require education and awareness. Above all, any solution requires the attention of the complacent masses who just want to get on with their life and click “OK” until they get what they want.